Wardialing and Other Phoney Stuff
Hacking around on the Internet before the Internet
Victorian Engineers built a vast network of copper cables and switching stations to relay text messages, and eventually two-way audio, between distant points. Sounds like Steampunk stuff, but it’s just the old Telegraph and Telephone systems that evolved into what we use today. (Also memo to self: The phrase “Victorian Engineers” sounds cool, needs to be used more often.)
The telephone system was the Internet before the Internet, providing a pretty impressive capability to connect everyone’s home to countless other homes and businesses across the globe. But you know: Invent a technology, and people will begin messing around with it, almost immediately. In my last article, I mentioned a not-well-known meeting between Thomas Edison, inventor of the Phonograph, and Oberlin Smith, inventor of magnetic recording. Oberlin’s account of this meeting included an offhand comment from Edison about how phonograph recordings could be played backward, and the phrase “mad dog” played backward would become something “unspeakable” (at least for that point in time)
The fact that the inventor of the phonograph was screwing around with it and having it create Victorian-era obscenities from a backward recording is pretty good evidence that hackery and general technological clowning-around dates back much further than the invention of computers and the internet.
It rarely makes it into the history books though, and if the first thing Alexander Graham Bell said to Watson over the phone was actually “Farts! Farts! Farts!”, we probably would never know.
Shenanigans safe to say though were going on not only before the Internet, but well before any of our times. If it is the telephone system we are talking about specifically however, I can fill in some shenanigan information, starting in the 1960’s.
Ma-Ma-Ma Bell, It Will Get You
We had a rotary-dial phone in the 1960s, and my earliest memories as a kid were about it being a “party line”. Simply put, multiple households shared the same telephone line, so you could actually pick up the phone and hear someone else having a conversation. So I guess an early “hack”, if you can call it that, was to eavesdrop on people sharing your line.
I was a little young to really be interested in what adults in other houses were talking about, but obviously, it was a popular pastime among people with party lines. There were some subtleties to it, like the fact you could hear someone on the same line pick up the receiver because it created an audible click, giving the eaves-dropees a chance to know they were being listened to.
Telephones had been around almost 70 years by the time I ever used one, but even so, the 1960s phone situation was still pretty limited in scope. Even if you did not have a party line, chances are you had just one, or at most two (wired) phone extensions in your house on a single line. Much of this was because the one company in the US providing phone service and equipment, the Bell Telephone Company, charged subscribers extra if they wanted additional phones in their homes.
Again I am not talking about multiple lines, just multiple phones on the same line. We lived in a two-story house and had an extension each floor. But in our finished basement, we also had a “ringer”, which was a box that rang when the phone rang, but was not a fully functioning phone. The ringer was a grey area, and source of contention between us and the phone company, because they would routinely test to see how many phones were on the line to try to catch people evading their extension fees.
When I was a kid I had no idea how this detection magic happened, but as an engineer I later figured out that this was a basic impedance test on the line from the central office, to see how many device loads were on it. All phones came from Bell Telephone Company at this point, so they all had the same characteristic impedance that divided down, the more of them were connected in parallel. This made figuring out how many extensions on a line a matter of simple math. Anyway, our ringer was probably not a sanctioned Bell product or paid-for third extension, so when the phone repairman came to visit he would disconnect it. And then, after he left, we would reconnect it.
Bell Telephone would run afoul of US anti-trust laws in the 1980s, and was broken up into eight separate companies. The landscape quickly changed (for the better, in my opinion anyway), with unrestricted extensions allowed on a line, wireless phones, and and a much expanded array of better phone products and services.
Do You Have Prince Albert in a Can?
The rotary-dial phone system back then was only mildly hackable in an electronic sense, because it was so computer-free. But I and my intrepid friend Dave spent some time as tweens engaging in the “Social Engineering” aspects of it — namely making prank calls. We by no means were pioneers here. The anonymity, or at least the perceived anonymity of the non-computerized and non-caller-ID phone system made hassling random strangers back then a staple of bored-kid life.
Before my time for instance was the joke of calling a store and asking “Do you have Prince Albert in a Can?”, referring to a popular tobacco product. When the store employee said, “Why yes!” the kid would reply with “Well you better go let him out!” and then hang up the phone. How fun!
We never did this one, because no one knew what the hell Prince Albert in a can was, even in the 1970s. I guess the more common version from my time was “Is your refrigerator running? / Better go catch it!”, which was equally lame, in our opinion anyway.
Our brand of phone pranks was more along the lines of gaslighting random people by calling and not identifying ourselves, and when they asked who it was, we’d reply “Oh come on! You know who this is!”, to try to elicit some guess. From thereon we would pose as that person, in an increasingly cringeworthy way until the person on the other end catches on, and we’d hang up.
This kind of social engineering hack has the same DNA as a modern-day phishing scheme, except our intent was always squarely centered in mayhem and not profit. Our phone imposter game eventually went a bit too far. One day I observed a line technician repairing a cable and using his belt-mounted handset to call the Operator, and then say something like “Hello Operator, this is Repair. Can I have ID please?” And in response, the Operator would tell the repairman what the phone number he was calling from was.
This was quite useful for isolating a line in a phone trunk cable that could have hundreds of twisted pairs, but this “feature” of Operator interaction had no other practical value. Twelve-year-old me was fascinated by telephone repairmen and their gear, however, and I also had a deep awe/fear of the legendary telephone Operator — who could always be reached by dialing zero, and whose powers included not just allowing you to make collect calls, but also being able to identify what number you had called from.
It didn’t stop us from trying the “Can I have ID please?” trick ourselves. In my best phone repairman voice, I dialed zero then made the request, and the Operator dutifully read back my phone number to me. I was delighted, and probably should have quit while I was ahead. But some time later I repeated the trick, and the Operator got suspicious of me this time (probably because it sounded like a 12-year-old calling) and asked me for my badge number. In a panic, I hung up. Then the phone rang, and it dawned on me only then that the Operator not only knew who was calling, but could call them back.
I think we ran out of the house at that point, and luckily no one else was home to take that Operator callback. We had somehow managed to take the almost completely anonymous phone system and find a way to mess with the one person on it who could identify us. Very Twelve.
Le Phreak, C’est Chic
In the 1960s the telephone system in the US would begin to migrate to electronic switching, which is where the dawn of computer hacking begins. (Remote hacking, that is - not discounting some mainframe hackery before this)
The phone system could now make connections automatically — but to do it, the primitive switching systems of the day communicated with one another using simple signaling tones, which could be copied by end-users of the system.
As the story goes, a 7-year-old blind boy named Josef Engressia accidentally discovered a key phone switching frequency, 2600 hertz, due to characteristics of his voice that kept disabling the phone recording feature he relied on. Transmitting this frequency on a line tricked the telephone switch into thinking the call had ended, but left the line open allowing it to be used for free long-distance calling.
Hacking around on the phone network like this became known as Phreaking, and spawned what might be the first underground hacker community. A guy named John Draper is considered to be an original and legendary Phreaker. Draper as it turns out was friends with Engressia, and learned of the 2600 frequency trick. Not having the same voice characteristics as Engressia, Draper needed a new way to generate the 2600hz signal, and found that a giveaway whistle in a Cap’n Crunch cereal box produced the exact needed tone. This discovery earned him the hacker nickname “Cap’n Crunch”, or alternatively “Crunchman”.
Side Note: I was surprised at some embarrassingly-late point to learn that the famous hacker publication 2600: The Hacker Quarterly was referencing the 2600hz tone. For some reason I was thinking Atari 2600.. must be the gamer in me
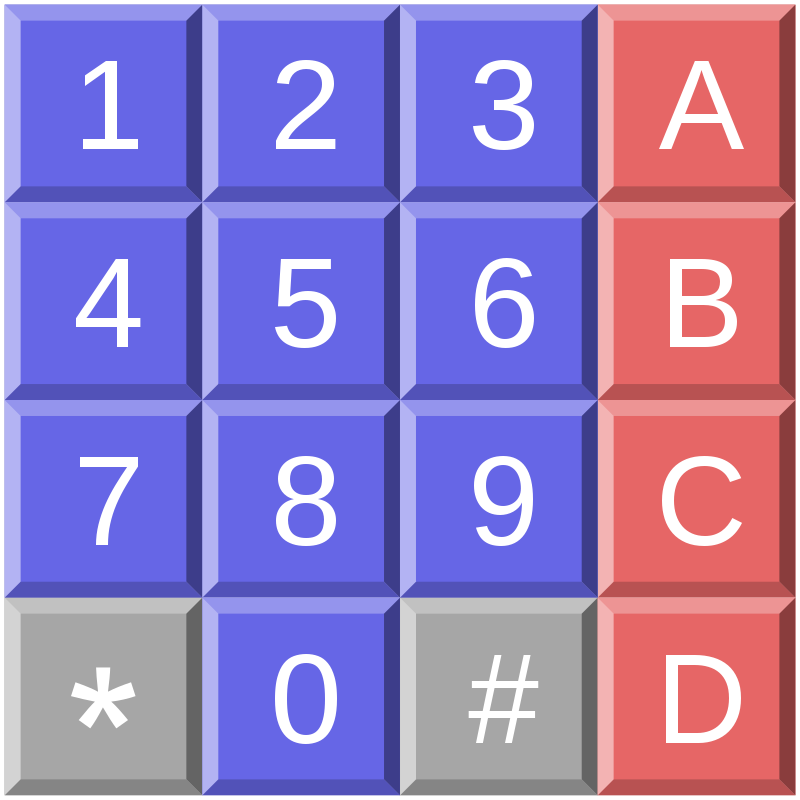
Things got more complex from here, when DTMF / “Touch-Tone” dialing came along. Now phone switching systems used multiple frequencies to signal call numbers and functions, and again the phone company relied on a pretty bad “security through obscurity” plan to keep people from abusing it. That went about how you would expect, with hackers building all sorts of specialized boxes to exploit the phone system.
Phreaking as a topic could easily consume multiple articles, but unfortunately not written by me, because I was not really active in this space. Although — I was fascinated with DTMF dialing, when I learned it was a combination of a “row” and “column” frequency on the keypad, and further that there was a secret missing A/B/C/D column of buttons with special functions. I may have built a full 16-key DTMF pad to try it back then, but not sure I got anywhere with it.
War Dialing For No Dollars
It seems the further forward you go in time, the less interesting phone hacking becomes, at least from my perspective. Caller ID and computer system logging made it a lot harder to do anything anonymously, and long-distance calling got cheap once the phone system broke up, making phone hacking less worthwhile. I know that early cell phones were not protected well and became a hacker target, and even now there are people active in that space. But it feels like once computer networks began to spring up in the 1980s, the general hacker community moved on.
The first computer networks were the dial-up kind, where you would use a modem on your telephone line to call another computer directly. Modem lines then were mostly for dedicated use by companies, and no public internet-like directory existed, at least at first. We are talking pre-AOL, and even BBSs were just getting started. This is where my only real foray into black-hat hacking happened.
There used to be an old TV show called Dialing for Dollars, where a host would call people up while showing a movie and if you were watching and answered, you would win cash. When I think about the term “Dialing” this show comes to mind for some reason, but in the case of my Wardialing adventures, no dollars were involved, just dialing hackery for the sake of it.
What is Wardialing, some of you might ask? Click the link for the full deal, but in short is the idea of using a modem and computer to call successive telephone numbers, searching for other modems. The name comes from a scene in the 1983 movie Wargames, but I swear I was already thinking of building one before seeing the movie. What the movie added for me was a cool GUI that displayed the list of numbers it found modems on.
When I was a sophomore in college in 1983, I built a war dialer for my VIC-20 computer and replicated this Wargames interface (like many others, apparently).
For the hardware geeks: This was basically just a relay connected to a 600-ohm transformer, that could replicate rotary style, pulse-code dialing. On the input side I had a 567 PLL tuned to the modem signal frequency, to detect a remote system. So a couple of I/O pins to the VIC only were needed. Total cost about $10 in Radio Shack parts. I stuffed the whole thing in an underarm deodorant spray cap that dangled off our dorm room wall phone.
My roommate at the time was a black belt in Karate and threatened to break bones I did not even know I had if I ran up the phone bill with my ‘demon dialer’, but fortunately for my bones, the bill was fine — in spite of leaving my VIC to dial hundreds of numbers while I was at class. Just like in the movie, it did end up finding dozens of open modems to connect to when I returned. When we called all of these, a surprising number of them had little or no security, connecting us directly to a system without any login needed. (This no-security thing was a topic of another article I wrote about the 80’s hacking scene)
We snooped around a lot but I don’t recall doing anything more malicious than that. A lot of school system computers, and some business office systems that seemed to contain stuff that I am sure they would be horrified to know random college engineering students were poking around in. A notable line I remember getting onto was something to do with a NOAA weather satellite system.
I like to think we just accessed some data dump from the satellite, it was mostly tables of numbers with no heading info to tell us what we were looking at. I don’t think we had any kind of direct link going on.. that is I think we didn’t… And hopefully, we did not mess up anything satellite-related there in our poking around. (If there were any storms in the fall of 1983 that strangely did not get tracked properly though, I have no comment.)
But just like in my twelve-year-old prank-calling days, we again took this scheme too far. After calling one number on the modem list and getting an initial tone but no further response, we hung up. And then the phone rang. We picked it up, and heard a modem tone from some unknown system, that had called us back! Memories of the fearsome Operator from my past were certainly in play here, as was the actual plot of Wargames, in which I believe the WOPR computer does something similar to Matthew Broderick.
Anyway we were very freaked out and followed the same playbook as twelve-me, and ran outta there. As if that would have actually helped, if we had started global thermonuclear war or something. I was maybe 19 then, and so it seems seven years is not enough time to improve your hacking emergency plans. It was only later that I learned about the concept of a “toll-saver” feature, which allowed one to make a brief call to a system, hang up, and then have it call you back to save you the long-distance charges. This is almost certainly what was going on here, but since it was 1982 and before caller ID and so on, this would likely have been a feature of perhaps a phone company system. Probably just as well we didn't mess with that one.
So I suspect that some of my readers might have their own tales of the phone system to share. Please do! It is easy for me at least to forget what a bygone era the whole phone world really is at this point and how it might be of interest to those who missed it. But I have faith that we’ve got some people out there who messed around with Ma Bell. In the end, if something is connected to something else, someone is going to hack it!
Explore Further
Next Time: Long before Command & Conquer, Steel Panthers, and Civilization there was Empire, a mainframe strategy game conceived in 1971 that would influence the computer wargame and strategy world for decades to come. I am very excited to bring readers a conversation I had recently with its creator, Walter Bright. So be sure to join us next week, as we talk about the pioneering days of computer game development!
The Mad Ned Memo covers topics in Computer Engineering and Technology over the past 40 years. Sign up and get nerdy tales and discussions of computing’s past, present, and future delivered straight to your inbox, and never miss an issue! (See the link for a sample selection of past articles) The Mad Ned Memo is cost-free and ad-free, and you can unsubscribe at any time.
The Mad Ned Memo takes subscriber privacy seriously and does not share email or other personal information with third parties. For more information, click here.